Okta
Summary
This short series of steps enables Okta admins to connect their Okta instances to Bigeye for single sign on. Bigeye supports SSO via OpenID Connect (OIDC). Upon completion, your employees will be able to login to Bigeye via Okta.
Note - substitute the email domain valuesMake sure to enter the same
<domain>value throughout this process. The domain will be the email domain of your users such asexample.com. If you have more than one domain, it is recommended to set up more than one connection inside of Bigeye.
Note - your Bigeye URL may be differentIf you use a Bigeye URL that is different from app.bigeye.com, please substitute your Bigeye URL while performing the steps of this configuration.
Part 1: In your Okta instance, set up a new application for Bigeye.
- As an Okta Administrator, in Okta, navigate to Applications.
- Click the Create App Integration button.
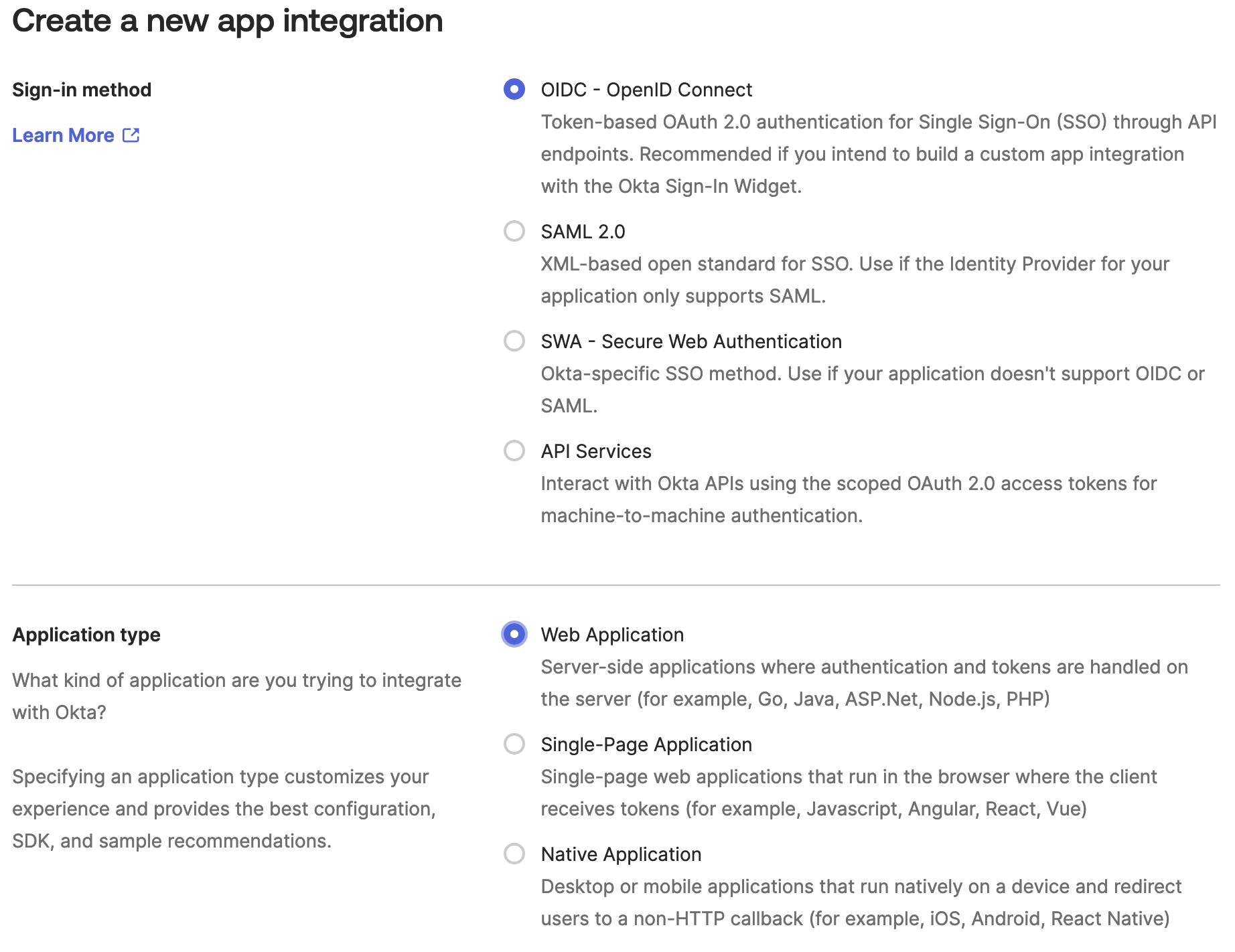
- Select OIDC �- OpenID Connect and Web Application, then click Next.
-
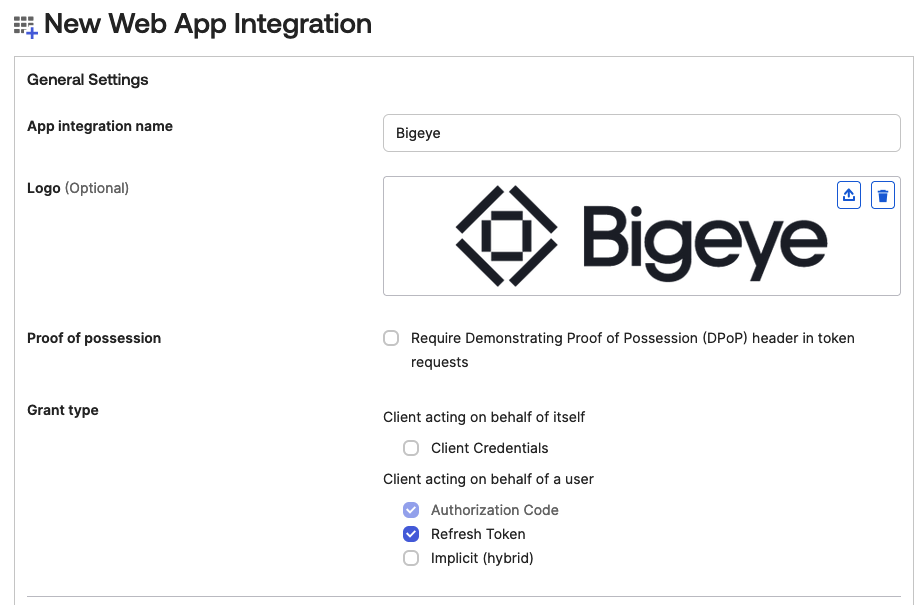
In the New Web App Integration section, enter an App Integration Name, set the Bigeye logo, and set the Grant Types to Authorization Code and Refresh Token:
-
Set
https://app.bigeye.com/sso/oidcLogin/<domain>as the Sign-in redirect URI:
-
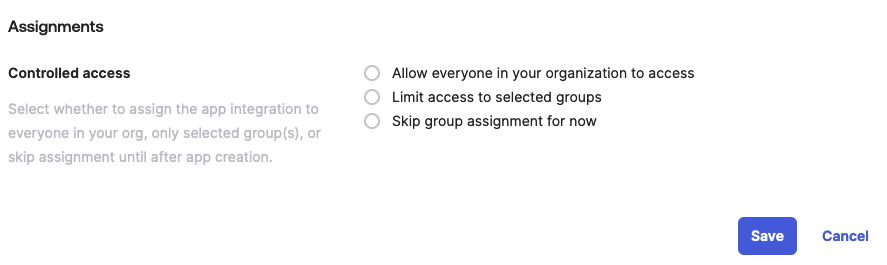
Select an Assignment and click Save.
-
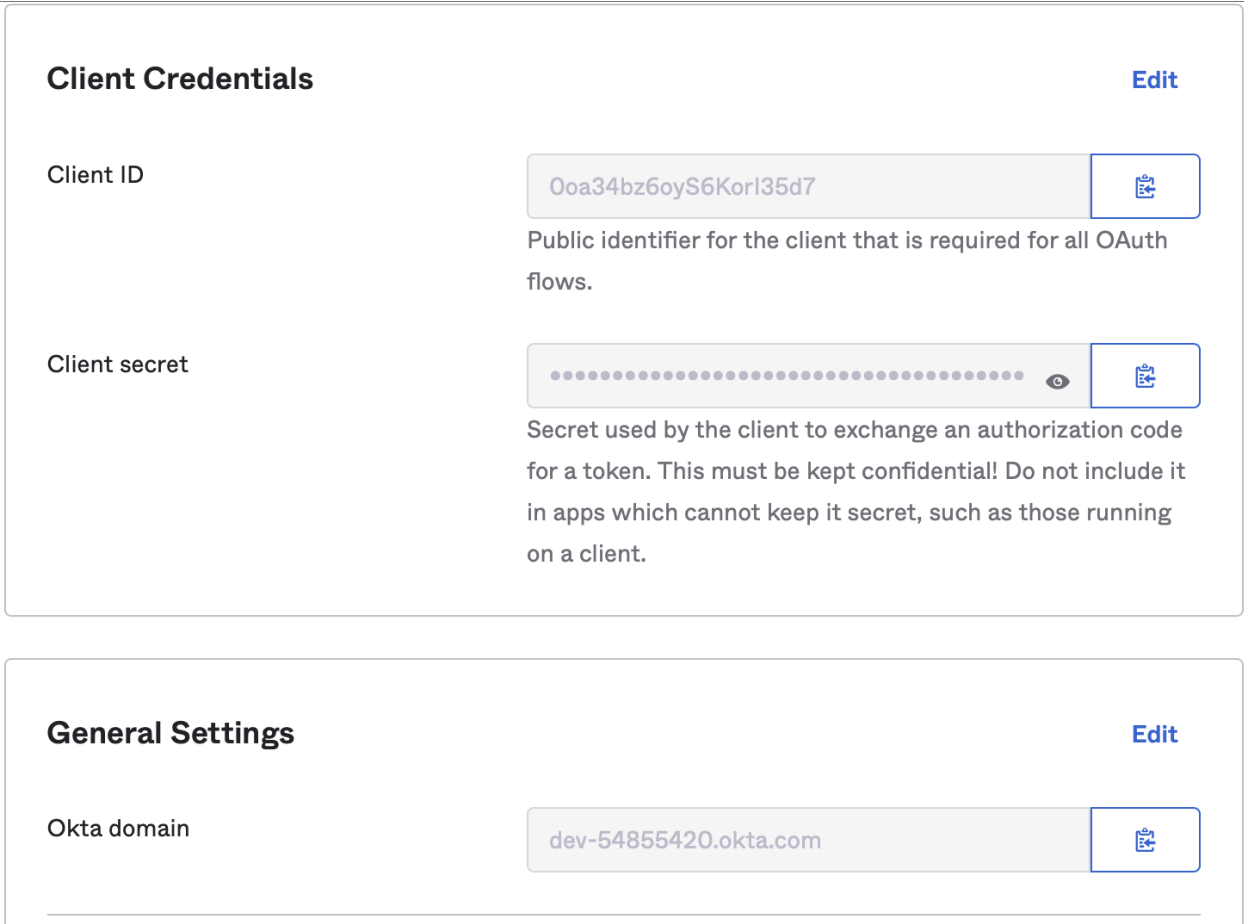
You will now see the General section of the application. Both the Client ID and the Client secret will need to be sent to Bigeye as part of the setup.
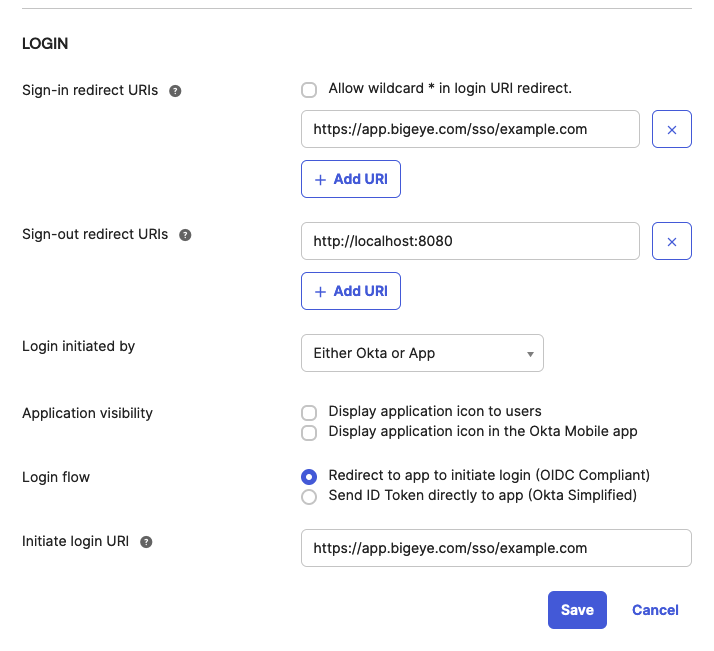
- To enable direct login from the Okta dashboard:
a. In the General Settings section, click Edit.
b. Scroll down to the Login section.
c. Change Login initiated by to Either Okta or App.
d. Set Application Visibility.
e. Enterhttps://app.bigeye.com/sso/<domain>in the Initiate login URI field.
f. Click Save.
Part 2: Create connection in Bigeye
- Go to https://app.bigeye.com/settings/single-sign-on
- Click New Connection
- Set the following values:
- Single sign-on provider: OpenID Connect (OIDC)
- Domain: your email domain (e.g. example.com). After this connection is activated, all email addresses for this email domain will be forwarded to your identity provider.
- Connection name: your email domain (e.g. example.com). This is an identifier used by Bigeye and your identity provider when they interact.
- Issuer URL: this is the URL that provides information about your OpenID Connect endpoints and which parameters are accepted. This URL should be accessible over the network that connects to Bigeye. Bigeye will append
.well-known/openid-configurationto the URL you provide. - Client ID and Client Secret as configured by your identity provider
- If you wish to use API keys with SSO users, make sure to add
offline_accessto the list of Scopes
- Click Save
Once the connection is saved, all logins for the domain specified will be validated by your identity provider. We highly recommend doing the following to verify your connection:
- Log in inside of another browser to verify that you can log in. If you are not able to log in, you may delete the Single Sign-on Connection inside of Bigeye to prevent other users from being locked out.
- Verify in your identity provider that the correct users are added to the applicable membership groups for Bigeye.
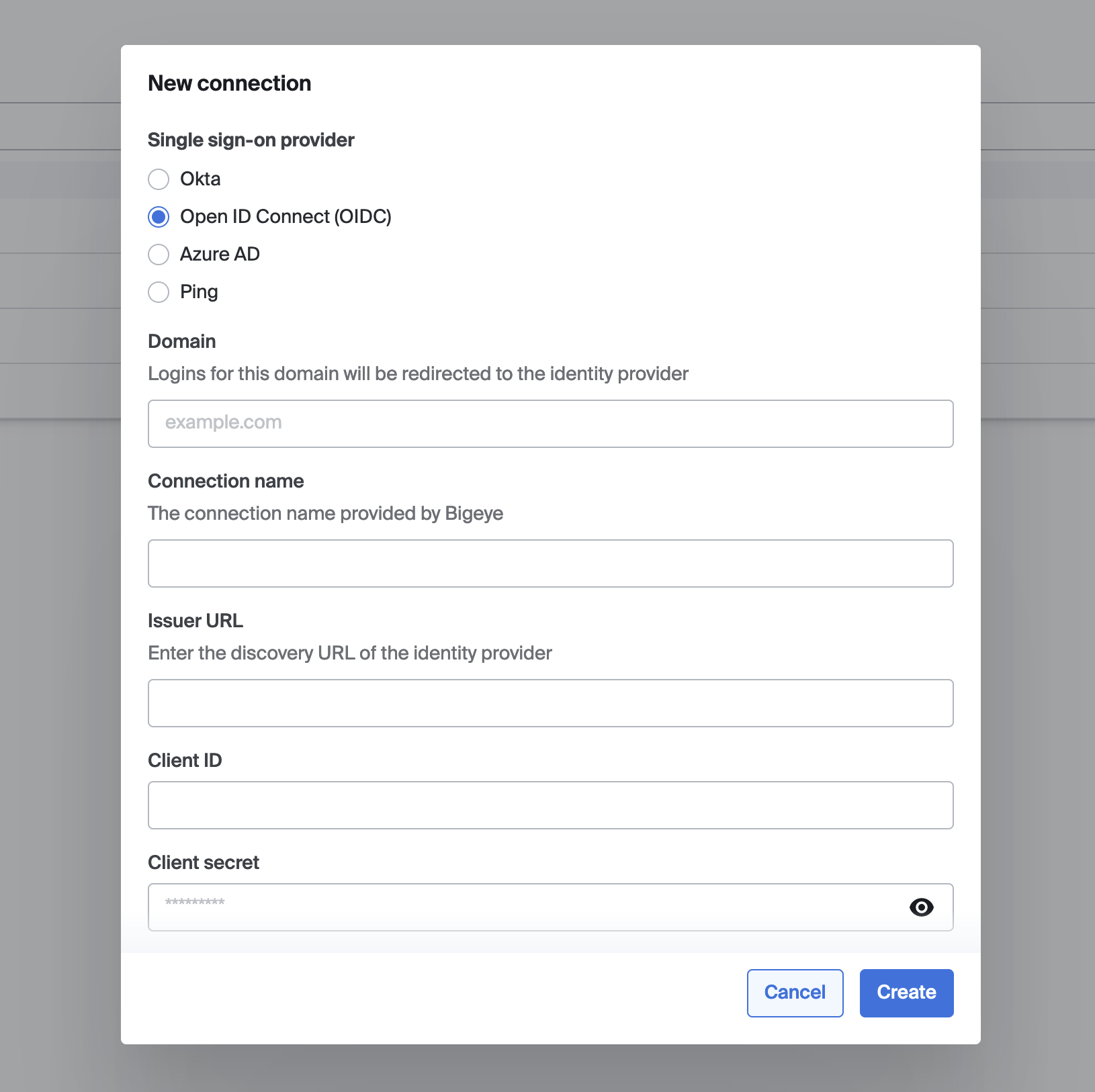
Configuration dialog for a new single sign-on connection
Updated 3 months ago
